On any given day, a developer at one of the world’s most sophisticated AI companies can accidentally push proprietary code to a public GitHub repository. It gets caught. It gets addressed. And it remains a precise illustration of something that no amount of AI capability has changed: security is not a technology problem. It is an accountability problem.
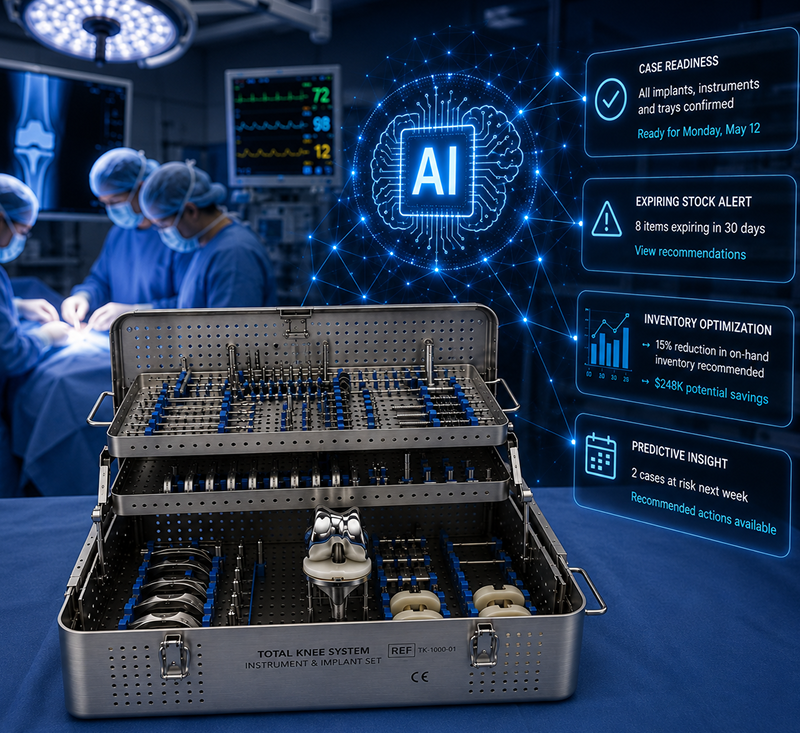
For Directors and VPs responsible for field sales, commercial operations, IT, and last-mile logistics at medical device companies, that distinction carries direct financial and regulatory consequence. The question is not whether AI can generate code or manage workflows faster than legacy systems. It can. The question is who stands behind the platform when something goes wrong with the data moving through your field organization every day, and whether the vendor running that platform has already answered that question at scale.
If you go back to the AI that wrote the code and tell it you leaked patient data, it will say 'I'm sorry.' That response is not a compliance posture. It is not a regulatory defense. And it will not protect your organization.
The Accountability Gap Is Not Closing
Every major AI coding platform carries the same disclaimer before you begin a session: AI can make mistakes. That language is not legal boilerplate. It is a deliberate statement about where the ultimate responsibility lies. Accountability has not transferred to the tool. It remains with the organization that deployed it and ran patient-adjacent data through it.
When a HIPAA violation occurs, regulators audit organizations, not models. They ask who owns the system, who reviewed it, who certified it, and who is responsible for the data it processed.
This is the accountability gap that no AI tool is positioned to close. Writing code faster does not create proper governance structures, audit trails, incident response procedures, or the organizational accountability that regulators require. Those have to be built, enforced, and owned by humans. The supply chain management platform a medical device company runs should be backed by an organization that has already done that work.
What HiTrust Certification Actually Means
HiTrust is frequently misunderstood as a technical certification that lives in a security architecture review or a penetration test report. It’s much more. Achieving HiTrust means the entire organization has been evaluated against a rigorous and continuously updated set of requirements.
An AI tool can’t earn the HiTrust certification on your behalf. A developer can’t inherit it from a cloud provider. And you can’t generate it with a prompt. You have to build the organizational discipline that sustains it, submit to the audit that validates it, and maintain the posture that renews it. For most medical device companies, that represents a multi-year organizational undertaking with permanent operational overhead attached.
Movemedical has completed that undertaking. HiTrust certification, SOC 2 compliance, and nearly two decades of operating in highly regulated markets are the foundation that makes our field inventory management platform safe to trust with the data that flows through a medical device commercial operation every day.
What Failure Looks Like in the Field
Abstract risk is easy to defer. Operational failure is not. For field sales & commercial operations leaders, the consequences of a compromised or unreliable medical inventory management systems are immediate and measurable: a rep arrives at a hospital for a surgical case with tray contents that don't match patient needs. Consignment inventory is miscounted, discrepancies surface, field teams lose visibility into trunk stock, product expires in the field, and case coverage drops. These are the operational realities that emerge when the platform governing last-mile logistics is not built to the standard the environment demands.
Add a data incident to that picture and the exposure compounds. A HIPAA violation tied to patient procedure data moving through a commercial operations platform triggers mandatory breach notification, regulatory investigation, and in most health system contracts, an immediate vendor review process. The financial cost of a single reportable breach routinely runs into seven figures. The reputational cost in a market where trust with hospital procurement takes years to build is harder to quantify and longer to recover.
What IT Owns When the Platform Wasn't Built to Last
For IT leaders evaluating platform decisions, there is a risk dimension that rarely appears in the initial build-versus-buy analysis: the long-term cost of owning a system built by AI or un-certified 3rd parties, and cannot fully be audited. An AI-generated platform managed by a small development team creates a specific and serious liability for the IT function that inherits it. There is a lack of expertise that arises at the foundational level, and those problems are magnified the more the system tries to scale, and can never become a true platform.
The developers who built the system carry the institutional knowledge that governs how it behaves. They know which rule sets were applied, which edge cases were handled manually, and which design decisions were made under time pressure. When those developers turn over, the next team inherits a system with incomplete documentation and no institutional memory of the choices that shaped it. Auditing that system, certifying it, or extending it becomes progressively more difficult. The IT function owns the risk without owning the knowledge.
This is distinct from what Movemedical's IT and security structure provides. The platform's behavior is deterministic and documented. The compliance posture is certified and auditable. When a health system's IT security team requests a vendor assessment, or when an internal audit requires a full accounting of data governance across the commercial operation, the answers exist and are verifiable. That is what IT ownership of a mission-critical platform should look like. It is also what domain expertise looks like — and it is not a feature that can be prompted into existence. It is the product of two decades of operational experience in a specific and demanding industry.
Why the AI Your Vendor Uses Is Not the AI Your Developer Uses
There is a meaningful and often overlooked difference between an AI agent and a domain-trained AI agent. A developer who opens an AI coding tool and asks it to build a field inventory management system is starting from a blank canvas. The tool has no knowledge of the workflows governing surgical case management, no understanding of how consignment models vary across health system contracts, and no experience with the compliance requirements that differ by country, region, and facility type. What gets built reflects the prompt rather than the domain.
Movemedical's AI agents start from a fundamentally different position. They are trained with nearly two decades of domain context: the workflows, the regulatory requirements, the operational patterns, and the field realities that come from running at scale across global markets. That context is not replicable by opening a new tab or hiring a capable development team. It is the product of sustained, focused investment in one of the most operationally complex commercial environments in healthcare.
Two organizations using the same underlying AI model are not using the same tool. In medical device field operations, context is the difference between a tool that approximates the domain and a platform that was built for it.
Platform vs Tool Selection Is a Risk Decision with a Financial Signature
Medical device companies that treat supply chain management systems as a tool rather than a platform selection, and as a cost decision rather than one of true ROI, eventually confront it as a risk decision. The financial signature of that confrontation is rarely small. Audit remediation following a compliance failure typically costs more than multiple years of platform licensing. A health system vendor review triggered by a data incident can stall or terminate commercial relationships that represent millions in annual revenue. And the internal cost of rebuilding or replacing a platform that was not built to scale compounds every quarter it goes unaddressed.
As field operations grow, as hospital relationships deepen, and as the volume of patient-adjacent data moving through commercial workflows increases, the compliance posture, security certifications, and accountability structures of the platform carrying that data become more consequential. A platform that functions adequately at fifty reps becomes a liability at five hundred if it was not built to the standard that scale requires.
Movemedical was built for that standard from its inception. The certifications, the domain expertise, the deterministic foundation, and the AI capabilities built on top are the result of two decades of focused investment in an industry with specific requirements. That is the difference between a trusted platform and a simple tool that appeared reasonable at the start.
Accountability is not a feature you can add later.
Movemedical offers a Field Inventory Management Value Assessment to help leading and emerging medical device companies understand how our compliance posture, security certifications, and domain-trained AI capabilities can protect your organization. Schedule your assessment and you’ll get a detailed roadmap of how you can achieve audit readiness and revenue visibility at scale.



















.png)



.svg)
.svg)
.svg)
.svg)


